Sitemap
A list of all the posts and pages found on the site. For you robots out there, there is an XML version available for digesting as well.
Pages
Posts
Future Blog Post
Published:
This post will show up by default. To disable scheduling of future posts, edit config.yml and set future: false.
Blog Post number 4
Published:
This is a sample blog post. Lorem ipsum I can’t remember the rest of lorem ipsum and don’t have an internet connection right now. Testing testing testing this blog post. Blog posts are cool.
Blog Post number 3
Published:
This is a sample blog post. Lorem ipsum I can’t remember the rest of lorem ipsum and don’t have an internet connection right now. Testing testing testing this blog post. Blog posts are cool.
Blog Post number 2
Published:
This is a sample blog post. Lorem ipsum I can’t remember the rest of lorem ipsum and don’t have an internet connection right now. Testing testing testing this blog post. Blog posts are cool.
Blog Post number 1
Published:
This is a sample blog post. Lorem ipsum I can’t remember the rest of lorem ipsum and don’t have an internet connection right now. Testing testing testing this blog post. Blog posts are cool.
portfolio
Image to Text Transformation With Maximum Text Generation Using Feedback-based RL
In this project, which is elaborated in the following image, the aim was to generate text from images using a combination of VLM, RL and a feedback-based mechanism.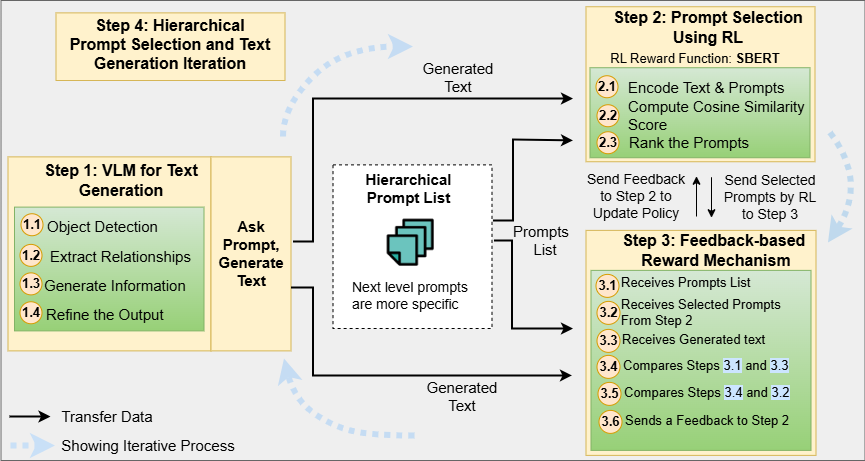
Using Mixture-of-Experts to Preserve Privacy
Generate text from images using VLM, MoE, RL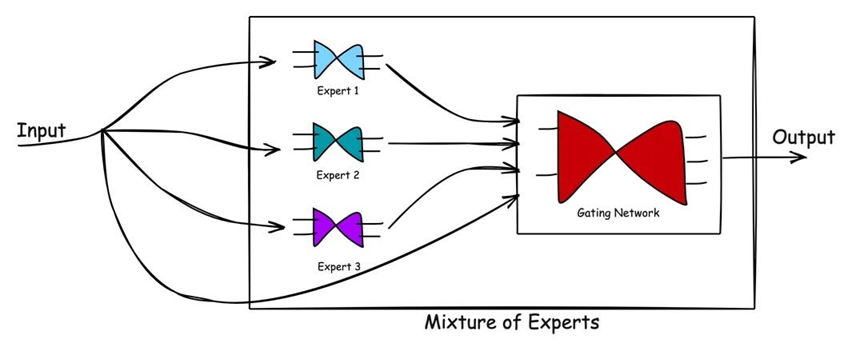
Credit Card Fraud Detection
Detecting credit card frauds using XGBoost and LightGBM methods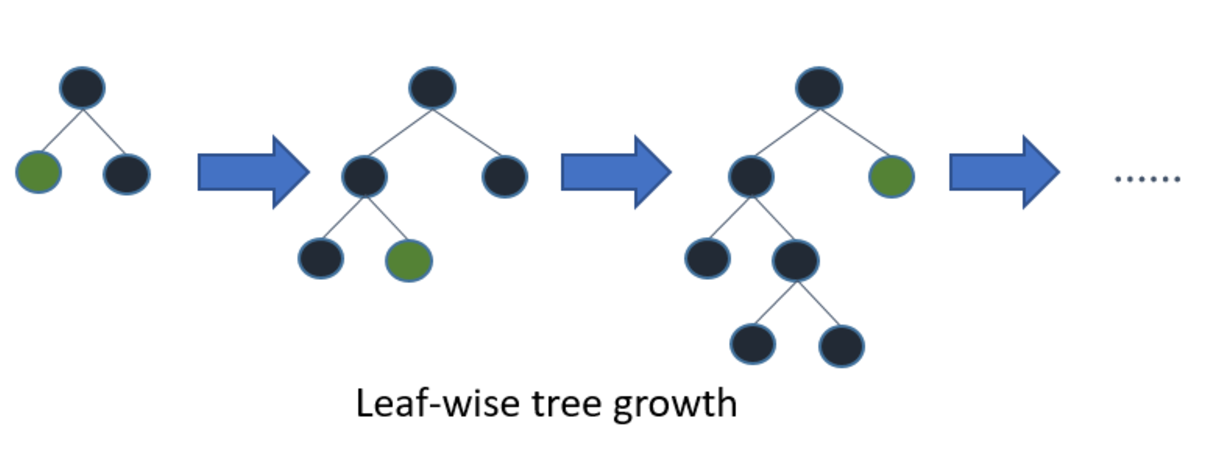
publications
Combination of Harmony Search and Linear Discriminate Analysis to Improve Classification
Published in 2009 Third Asia International Conference on Modelling & Simulation, 2009
An appropriate pre-processing algorithm in classification is not only of great importance with respect to classifier choice, but also would be more crucial. In this paper, a pre-processing step is proposed in order to increase accuracy of classification. The aim of this approach is finding a transformation matrix causes classes to be more discriminable by transforming data into the new space and consequently, increases the classification accuracy. This transformation matrix is computed through two methods based on linear discrimination. In the first method, we use class independent LDA to increase classification accuracy by finding a transformation that maximizes the between-class scatter and minimizes within-class scatter using a transformation matrix. Because LDA cannot obtain optimal transformation, in the second method, harmony search is used to increase performance of LDA. Obtained results show that utilization of these pre-processing causes increasing the accuracy of different classifiers.
Recommended citation: H.Moeinzadeh, E.Asgarian, M.Zanjani, A.Rezaee, M.Seidi. "Combination of Harmony Search and Linear Discriminate Analysis to Improve Classification." 3th IEEE International Conferance on Modelling & Simulation, Baundung, Indonesia, 2009.
Download Paper
Improving Classification Accuracy Using Evolutionary Fuzzy Transformation
Published in Proceedings of the 11th Annual Conference Companion on Genetic and Evolutionary Computation Conference: Late Breaking Papers, 2009
Selection of a classifier is only one aspect of the problem of data classification. Equally important (if not, more so) is the pre-processing strategy to be employed. In this paper, a pre-processing step is proposed in order to increase accuracy of classification. The aim of this approach is finding a transformation matrix to discriminate between classes by transforming data into a new space. Obviously, this tends to increase the classification accuracy. This transformation matrix is computed through two evolutionary methods (GA and PSO) using fuzzy approach with the aim of increasing membership degree of data to their classes by transforming them into a new space. The transformation matrix is independent of classifier and classifier type has no effect on computation of transformation matrix. Obtained results show that these pre-processing methods increase the accuracy of different classifiers.
Recommended citation: H.Moeinzadeh, B.Nasersharif, A.Rezaee, H.Pazhoumand-dar. "Improving Classification Accuracy Using Evolutionary Fuzzy Transformation." 11th Annual Conference on Genetic and Evolutionary Computation Conference (GECCO), Montreal, Canada, 2009.
Download Paper
Anomaly Detection in Online Social Networks Using Structure-Based Techniques
Published in 8th International Conference for Internet Technology and Secured Transactions (ICITST-2013), 2013
Online Social Networks as new phenomenon have affected our life in many positive ways; however it can be considered as way of malicious activities. Identifying anomalous users has become a challenge and many researches are conducted but they are not enough and in this paper we propose a methodology based on graph metrics of online social networks. The experimental results illustrate that majority of friends in online social networks have common friends with their friends while anomalous users may not follow this fact.
Recommended citation: Rezaei, A., Kasirun, Z. M., Rohani, V. A., & Khodadadi, T. (2013, December). Anomaly detection in online social networks using structure-based technique. In 8th International Conference for Internet Technology and Secured Transactions (ICITST-2013) (pp. 619-622). IEEE.
Download Paper
Credit Card Fraud Detection Using Tree-Based Algorithms for Highly Imbalanced Data
Published in 2024 IEEE 3rd International Conference on Computing and Machine Intelligence (ICMI), 2024
The escalation of cybercrime in recent years, moves on by the proliferation of electronic devices, poses a significant threat as users engage in diverse online activities, including financial transactions. Cybercriminals exploit phishing information and manipulate cardholders account balances to illicitly appropriate funds, presenting challenges in traceability. This study addresses detecting fraudulent banking transactions within customers account data, characterized by highly imbalanced fraud records. Employing diverse machine learning algorithms, particularly focusing on tree-based approaches, this research re-veals that LightGBM and XGBoost exhibit superior performance, with LightGBM demonstrating notable supremacy. The resultant evaluation metric, the Area Under the Curve (AUC), attains a commendable value of 0.94649, underscoring the efficacy of the proposed machine learning models in cybersecurity measures against fraudulent financial activities.
Recommended citation: Rezaei, A., Yazdinejad, M., & Sookhak, M. (2024, April). Credit Card Fraud Detection Using Tree-Based Algorithms For Highly Imbalanced Data. In 2024 IEEE 3rd International Conference on Computing and Machine Intelligence (ICMI) (pp. 1-6). IEEE.
Download Paper
RL-MoE: An Image-Based Privacy Preserving Approach In Intelligent Transportation System
Published in The 7th IEEE International Conference on Cognitive Machine Intelligence (CogMI-2025), 2025
Vehicular computing is vital to modern transportation, enabling real-time data collection for improved traffic flow, mobility, and safety. However, the widespread use of roadside cameras and IoT devices raises significant privacy concerns, as sensitive vehicular and environmental data are often transmitted. To address these issues, this paper introduces RL-MoE, a privacy-preserving framework that combines Reinforcement Learning (RL) with a Mixture of Experts (MoE) model. Instead of transmitting raw images, RL-MoE extracts textual descriptions from camera feeds, significantly reducing privacy risks. The MoE component uses specialized experts to generate summaries based on structured prompts, while the RL module optimizes these descriptions for accuracy and relevance. The framework also includes explainability methods to ensure transparency and trust. Experimental results show that RL-MoE effectively protects user privacy, enhances data transmission efficiency, and supports compliance with privacy standards. This study demonstrates how AI techniques can balance effective traffic monitoring with robust privacy safeguards in Intelligent Transportation Systems.
Recommended citation: Rezaei, A., & Sookhak, M., Medrano, C.R. RL-MoE: An Image-Based Privacy Preserving Approach In Intelligent Transportation System. 3rd USENIX Symposium on Vehicle Security and Privacy (Under Review).
Download Paper
Privacy-Preserving in Connected and Autonomous Vehicles Through Vision to Text Transformation
Published in IEEE Access (Under Review), 2025
Connected and Autonomous Vehicles (CAVs) rely on a range of devices that often process privacy-sensitive data. Among these, roadside units play a critical role particularly through the use of AI-equipped (AIE) cameras for applications such as violation detection. However, the privacy risks associated with captured imagery remain a major concern, as such data can be misused for identity theft, profiling, or unauthorized commercial purposes. While traditional techniques such as face blurring and obfuscation have been applied to mitigate privacy risks, individual privacy remains at risk, as individuals can still be tracked using other features such as their clothing. This paper introduces a novel privacy-preserving framework that leverages feedback-based reinforcement learning (RL) and vision-language models (VLMs) to protect sensitive visual information captured by AIE cameras. The main idea is to convert images into semantically equivalent textual descriptions, ensuring that scene-relevant information is retained while visual privacy is preserved. A hierarchical RL strategy is employed to iteratively refine the generated text, enhancing both semantic accuracy and privacy. Evaluation results demonstrate significant improvements in both privacy protection and textual quality, with the Unique Word Count increasing by approximately 77% and Detail Density by around 50% compared to existing approaches.
Recommended citation: Rezaei, A., & Sookhak, M., & Patooghy, A. Privacy-Preserving in Connected and Autonomous Vehicles Through Vision to Text Transformation.
PEFT-DML: Parameter-Efficient Fine-Tuning Deep Metric Learning for Robust Multi-Modal 3D Object Detection in Autonomous Driving
Published in AAAI-26, 2025
This study introduces PEFT-DML, a parameter-efficient deep metric learning framework for robust multi-modal 3D object detection in autonomous driving. Unlike conventional models that assume fixed sensor availability, PEFT-DML maps diverse modalities (LiDAR, radar, camera, IMU, GNSS) into a shared latent space, enabling reliable detection even under sensor dropout or unseen modality–class combinations. By integrating Low-Rank Adaptation (LoRA) and adapter layers, PEFT-DML achieves significant training efficiency while enhancing robustness to fast motion, weather variability, and domain shifts. Experiments on benchmarks nuScenes demonstrate superior accuracy.
Recommended citation: Rezaei, A., & Sookhak,. PEFT-DML: Parameter-Efficient Fine-Tuning Deep Metric Learning for Robust Multi-Modal 3D Object Detection in Autonomous Driving.
Parameter Efficient Hybrid Transformer (PEHT) for Network Traffic Prediction via Dynamic Urban Congestion Integration
Published in VTC-26, 2026
Accurate network traffic prediction is critical for efficient resource allocation in dynamic urban environment with cellular networks and mobile devices, there have been challenges due to the complexity of the city traffic. This paper introduces Parameter-Efficient Hybrid Transformer (PEHT) as a novel framework that integrates real-time mobility into a Transformer-based network traffic prediction model. PEHT separates primary network communication features from secondary city traffic features and uses Low-Rank Adaptation (LoRA) within the Transformer encoder to significantly reduce the number of trainable parameters in order to maintain high predictive accuracy. A multimodal fusion strategy injects external traffic features into a Decoder using more traffic data. Extensive experiments on the Telecom Italia Milan dataset and multiple synthetic congestion scenarios demonstrate that PEHT outperforms state-of-the-art models in terms of RMSE, MAE, and R^2 metrics.
Recommended citation: Rezaei, A., & Sookhak,. Parameter Efficient Hybrid Transformer (PEHT) for Network Traffic Prediction via Dynamic Urban Congestion Integration.
GraphTrafficGPT: Enhancing Traffic Management Through Graph-Based AI Agent Coordination
Published in Elsevier-26, 2026
LLM-based traffic management systems such as TrafficGPT rely on chain-based architectures that process tasks sequentially, reload context at each step, and handle only one query at a time. These constraints, rooted in the linear structure of chain-of-thought prompting, become especially costly for the multi-step, interdependent tasks common in real traffic management centers, where operators routinely monitor congestion patterns, signal timing, and incident response simultaneously. GraphTrafficGPT restructures this process around a directed acyclic graph: tasks become nodes, dependencies become edges, and independent tasks execute in parallel. A centralized Brain Agent (responsible for query decomposition, dependency analysis, and agent coordination) dispatches work to six specialized agents covering data retrieval, traffic analysis, visualization, SUMO-based simulation, workflow optimization, and general queries. Rather than reloading full context at each step, the system propagates only the information each downstream task requires, which appears to account for the majority of the observed efficiency gains. In experiments against the original TrafficGPT on a standardized set of traffic management queries, this architecture reduced token consumption by 50.2%, improved average response latency by 19.0%, and supported simultaneous multi-query execution with efficiency gains of up to 23.0%; however, simple visualization tasks, where graph construction overhead exceeds parallelization benefits, saw latency increases of 36–40%.
Recommended citation: Ferhat, N., Rezaei, A., & Sookhak,. PEFT-DML: Parameter-Efficient Fine-Tuning Deep Metric Learning for Robust Multi-Modal 3D Object Detection in Autonomous Driving.
talks
Talk 1 on Relevant Topic in Your Field
Published:
This is a description of your talk, which is a markdown file that can be all markdown-ified like any other post. Yay markdown!
Conference Proceeding talk 3 on Relevant Topic in Your Field
Published:
This is a description of your conference proceedings talk, note the different field in type. You can put anything in this field.
teaching
Design and Analysis of Algorithms
Course, University of Applied Sciences, 2022
Complex algorithms and problem-solving methods were taught and discussed in this course including recursive functions, dynamic programming etc.
Software Engineering
Grad Course, University of Applied Sciences, 2022
The course was offered to undergrad and graduate students of computer science department.
Python Programming
Undergrad course, Texas A&M University Corpus Christi, Computer Science, 2024
Teaching python programming language to undergrad students.
